RED TEAM
Wardriving: Red Team Research

Introduction
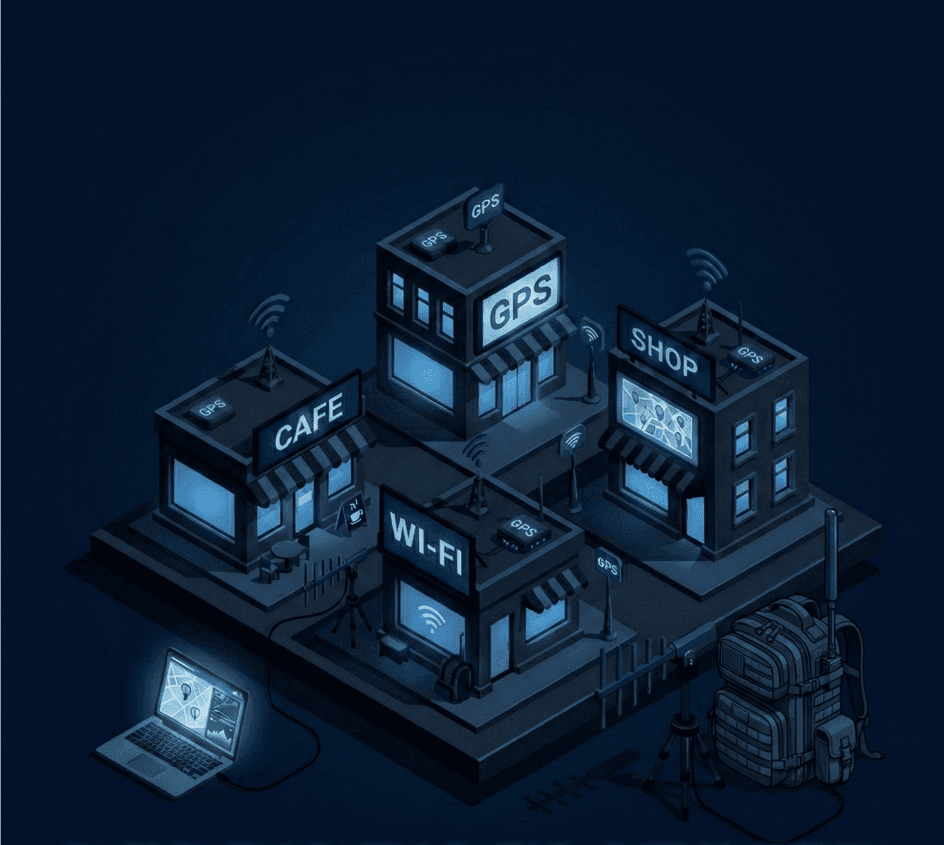
To create an actual attack surface, we are all already agreed on the fact that reconnaissance is the key to it. And it is a topic that has a very deep dive into it. There must be multiple ways to collect the most data possible to create an actual surface. One of these is wardriving. So, this article is about what wardriving is and what are the different methods of it.
Wardriving
Wardriving is a wireless technique to discover and map the most Wi-Fi access points possible while continuously roaming around the target area. This is the most common definition, but it is not limited to Wi-Fi. We will get to this point later on this article.
Wi-Fi
Wi-Fi has a wide place in the cyber world. Wireless protocols remain a critical vector for initial access because they are one of the doors between attackers and the systems.
Here are the reasons:
Gaining Access: On red team tests, post-exploitation is a very important part, but it means nothing without any initial access. Attackers try to get into the same network as their victims in order to operate their actions. But an attacker needs to find access points whether it is hidden or not (It is also possible to expose the SSID of hidden networks.).
Credentials: Gaining access is the beginning of any internal behavior. If we are talking about networks, an attacker needs credentials to be a part of the network. Wardriving comes to our rescue at this part because an attacker can manage attacks like “Evil Portal” or “Evil Twin” across the area to get as many credentials as they can.
Here are some ways of Wi-Fi wardriving:
Kismet
For Linux users Kismet is a great option to perform wardriving. Kismet can be used for Wi-Fi, Bluetooth, RF, ADSB airplane beacons and many more. This makes this tool very useful for these types of attacks. It is also compatible with remote devices, and this is the key feature that can be used in wardriving which is an another topic included in this article.
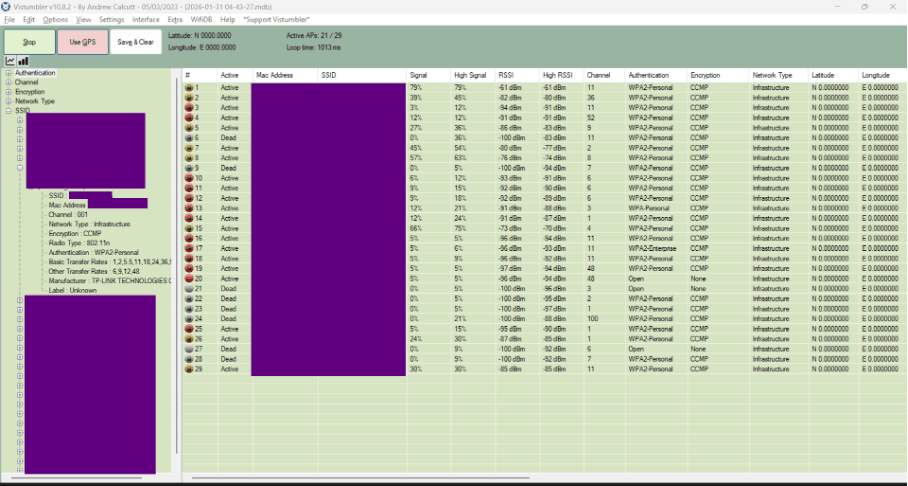
Vistumbler
Vistumbler is a Windows-Based tool to collect all the SSID’s (hidden or not) that your Wi-Fi card is able to see. Along with SSID’s, it also gives information like signal strength, channel and the authentication type of the AP. With the “Use GPS” button, it locates the geolocation of the AP too. There are also other tools like WiGLE etc.
But how to get some credentials?
Pwnagotchi
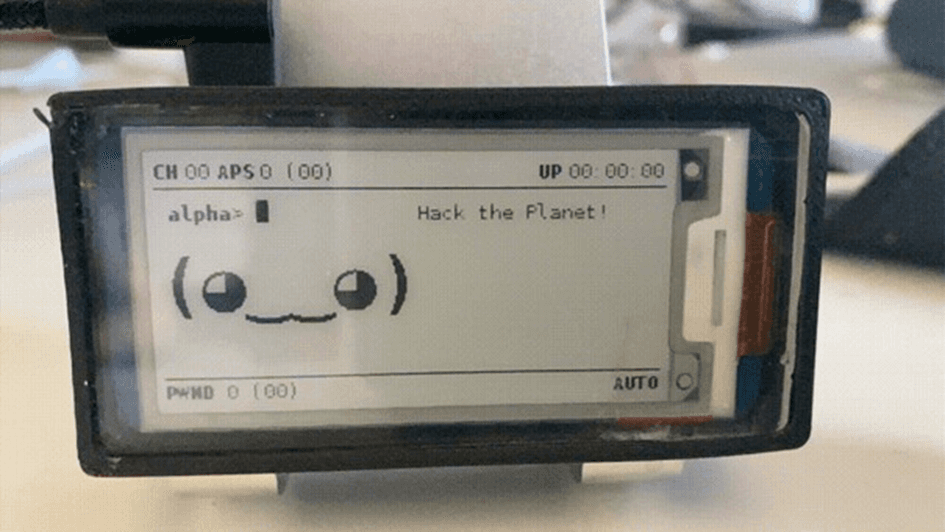
Pwnagotchi is an easy-to-build IOT project to collect all the Wi-Fi handshakes around (based on the power of the Wi-Fi card and antenna.). Because of its little size, it is much easier to carry around. So this makes it one of the most suitable gadgets for wardriving.
Fluxion
Fluxion is a Wi-Fi hacking tool that can also create captive portals and evil twin attacks.
But because our topic is not Wi-Fi hacking, I will skip the demonstration for it. There are so many different tools for these types of attacks. The man goal here is to get as many credentials as we can.
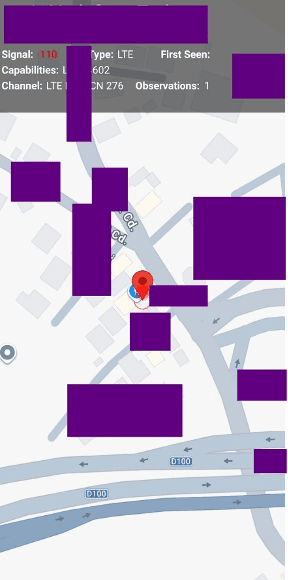
GPS
GPS wardriving is combined with the Wi-Fi or Bluetooth protocols, and it is used to get the exact location of every SSID. Because there are so many SSID’s, an attacker needs their exact location to choose their best target. This is important because an attacker’s first goal is to get initial access from the target or be as close as possible to manage further actions.
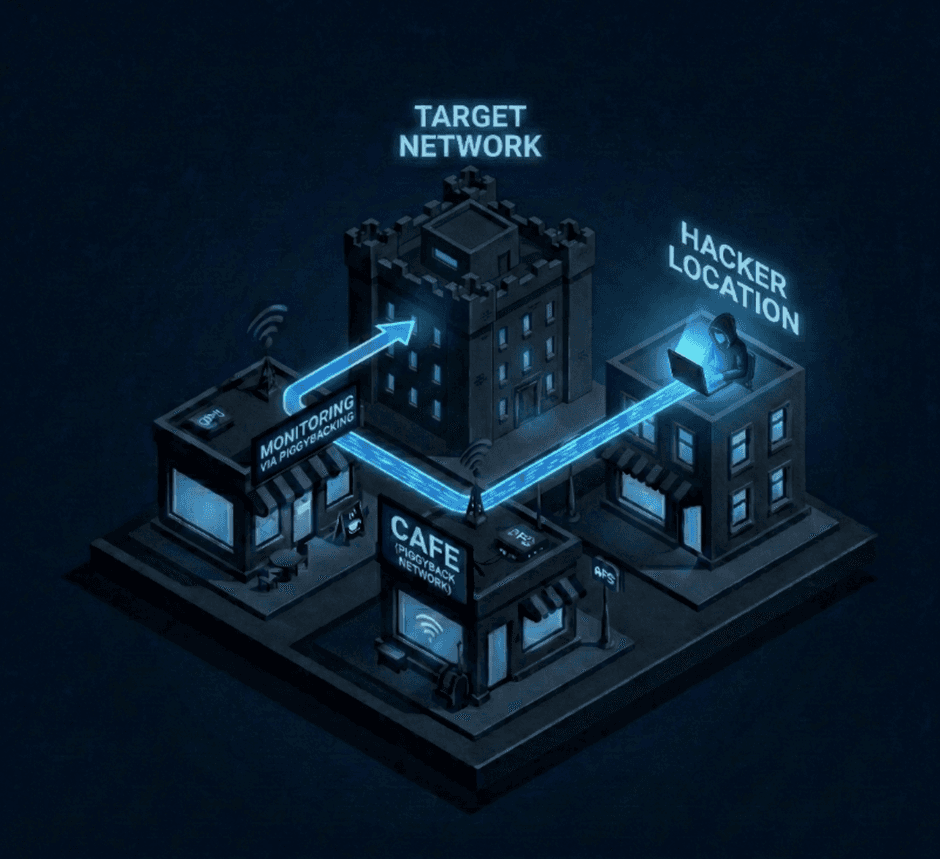
Piggybacking
In Cyber Security piggybacking is a term of using unauthorized networks. In authorized tests this is not used for obvious reasons. But in illegal activities, attackers are using the compromised network as a jump-box to the victim network. This is used like a real-life VPN and keeps their activities more anonymous.
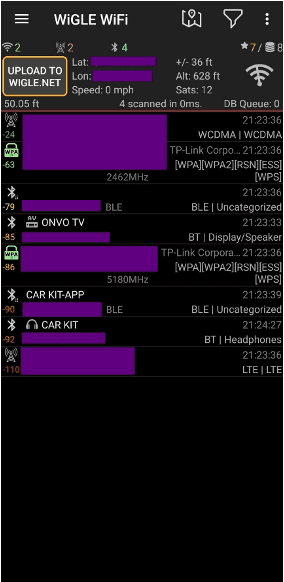
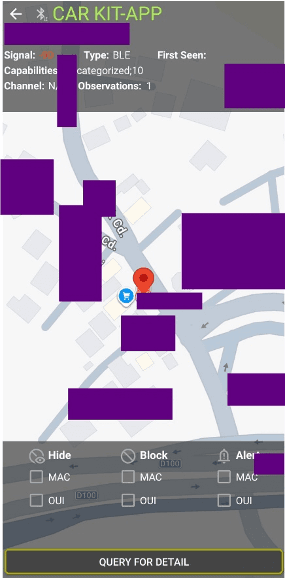
WiGLE
WiGLE is a tool running with google services on the background and it is a perfect app for mobile devices. WiGLE is not only detecting Wi-Fi networks but also looking for Bluetooth devices along with their geolocation. Even the location of a Bluetooth device can be used for any hacktivity.
Bluetooth devices are running on so many things including cars, TVs or keyboards etc. So, this means that hackers can track cars by locating them on the map. Or as the same on Wi-Fi networks, attackers can also create fake Bluetooth keyboards to manage evil keyboard attacks. With an external better GPS device attached to the device, it will discover much more devices on the map.
 |  |  |
BASE STATIONS
Base stations are central connection points that transmit and receive radio signals to bridge the gap between wireless devices and the main wired network. Because wardriving is operated in a wide range of area, this is a great opportunity for attackers to collect important data.
Tricking something into your own goal is a typical attacker behavior. To manage this, creating fake connection points would be an absolute winner.
IMSI Catchers
Other known as Stingrays, these are devices to perform MITM (man-in-the-middle) attacks but for cellular network traffic. But it is more complicated than this.
Originally, "Stingray" was a brand name of a device manufactured by the Harris Corporation for law enforcement, but the name has become a generic term for any fake cell tower used for spying.
IMSI stands for international mobile subscriber identity. Every mobile device using cellular data has this number. And it represents a unique number for every user in the cellular network. IMSI catchers are built to catch these numbers. Then attackers tell these numbers (devices) to remove the encryption in their traffic. So now an attacker can manage the traffic from the victim, flow from his own connection point first. We can say that it is a fake base station created by the attacker. By this, the attacker can now intercept the victim’s traffic. But this is not our main topic for now. But it has a very special place for wardriving.
Hackers are aggressively roaming the area to let them connect to their own “base station”. At the end of the day, the attacker will have so much data to continue the attack.

But there is a way to protect ourselves from this:
The vulnerability exists in cellular networks (especially 2G) because of the lack of mutual authentication. No one really knows why. Because of the lack of encryption in 2G, and most Stingrays (IMSI Catcher) are unable to crack the encryption of 4G/5G, hackers jam the 4G/5G frequencies forcing your phone dropping down to 2G. This is called as “Downgrade Attack”. As a result, hackers can easily read the intercepted data. So, simply disabling 2G would be a very good defense mechanism against these kinds of attacks.
These are the methods that attackers are using while wardriving.
There are hacking gadgets that can be used for these types of attacks:
Gadgets
Drones
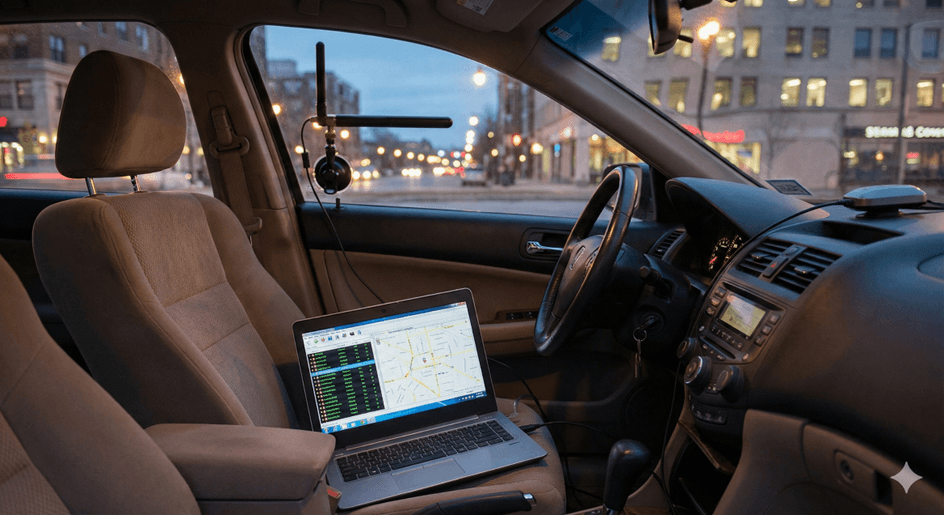
Wardriving also includes non-human interaction. Hackers can use vehicles like cars or aerial vehicles like drones to improve the level of anonymity. But this idea brings this question: How to perform these actions using a drone?
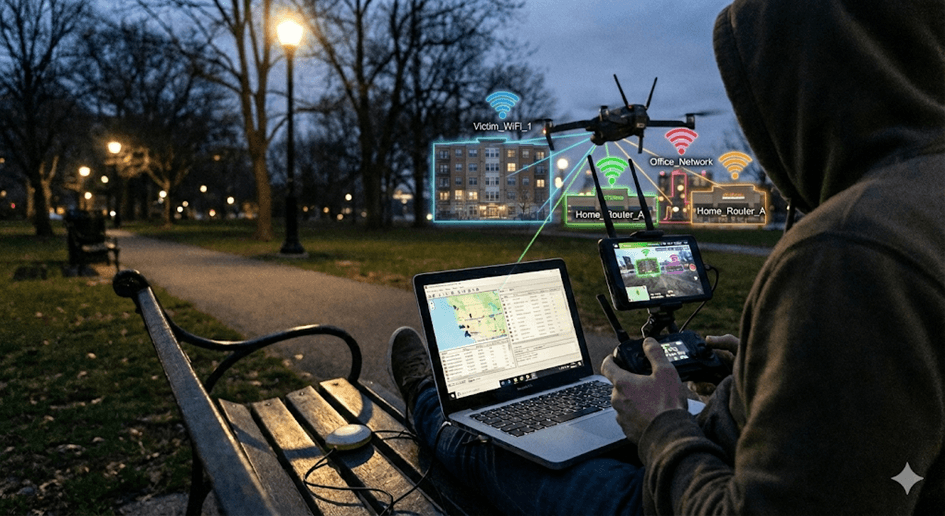
Attackers are integrating a single-board computer like Raspberry Pi to a drone with a good Wi-Fi adapter and a GPS module to gather and steal information like Wi-Fi handshakes, SSIDs and the location of every kind of device that has an active connection to Bluetooth or Wi-Fi.
Using Kismet with a Drone
On actions that must be performed in large areas, controlling the attack remotely takes a very important place. Kismet has a very useful package in its documentation named “kismet_drone”. This package is built to run on remote devices.
Combining a drone with a Raspberry Pi, then installing a strong Wi-Fi antenna and a GPS module would work perfectly with the variety of attack vectors on Kismet. By remotely controlling it from the air, the chance of getting caught will be more difficult for attackers.
Flipper Zero

Flipper is a Swiss-knife of a hacker that can do things like opening gates or barriers remotely. And it also includes things like Sub-Ghz, Infrared and much more. The good thing here is that we can update this gadget with external hardware. Because of its pocket size, this makes it one of the most suitable devices for wardriving.
HackRF

HackRF is an SDR (software defined radio) to send and receive signals. A hacker will be able to analyze spectrums, this means HackRF allows an attacker to visualize hidden signals that aren't Wi-Fi or Bluetooth. This great gadget can be used to listening or sending data to different frequencies.
Kali Nethunter (Mobile)
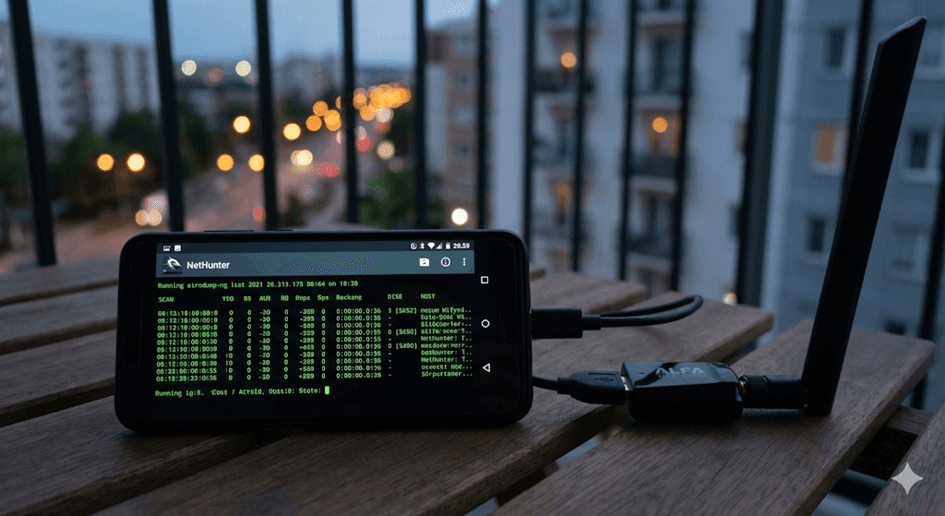
It is also possible to perform with a Kali NetHunter installed phone because of its high mobility and the easy carrying size of a phone. With its default installed tools, it is much easier to manage everything.
How To Protect Our Data?
Setting up WIDS (Wireless Intrusion Detection Systems) to detect deauthentication frames is a good start to prevent an attack. Using hidden SSIDs would also slow down any activity. If the system does not need to be external, setting up the network internal is always the best idea.
Setting up Faraday cages for signal shielding is also a very strong defense mechanism against any kind of attack.
Disable 2G connection would not be enough for any IMSI catching attack. So, setting up VPN tunnels is also a useful way to prevent any data interception.
According to the sensitivity of the data, avoiding the use of any unnecessary connection on a device is very important at this point. This can be a simple Bluetooth connection or an insecure network that is open to public or even a specific frequency that is way too old for its time.
As Zerone Security our mission is to protect your data, even if the threat comes right up the air.
Conclusion
Wardriving is a good method for an offensive tester to gain information. It is effective for target-hunting attacks because of its extended range of usage. It does not only consist of Wi-Fi reconnaissance but also includes technologies like Bluetooth, GPS, cellular networks etc.




